Real-time file encryption
Files placed inside a locker are encrypted immediately, helping protect local data and cloud-bound content before it leaves your device.
See encryption flowTrusted by millions • Colorful privacy-first design
Folder Lock helps secure files and folders with AES 256-bit encryption, private lockers, portable encrypted containers, secure sharing, and cloud-safe workflows. This landing page turns a security product into a clear, user-friendly experience with technical explainers anyone can follow.
Built for privacy-minded users who want clarity, speed, and control.
Why Folder Lock stands out
Instead of dumping technical jargon on visitors, this page uses a modular layout to show what Folder Lock does, why it matters, and how its privacy workflow behaves in real use.
Files placed inside a locker are encrypted immediately, helping protect local data and cloud-bound content before it leaves your device.
See encryption flowPrefer hiding content over encrypting it? Folder Lock also offers folder and drive protection designed to make items inaccessible and hidden.
See the protection pathCreate a protected container you can carry on removable media and open on another system with the right password.
Explore locker typesUse encrypted lockers alongside Dropbox, Google Drive, and OneDrive so your backups stay private even during sync.
Explore cloud lockersShred sensitive files, wipe empty space, and clear Windows history traces that users often forget to remove.
Jump to safeguard toolsStore passwords, banking details, notes, and personal data in encrypted secret records instead of loose text files.
Explore secretsHow it works
Click each step to see what happens behind the scenes when a file moves from your desktop into a protected locker and then to the cloud.
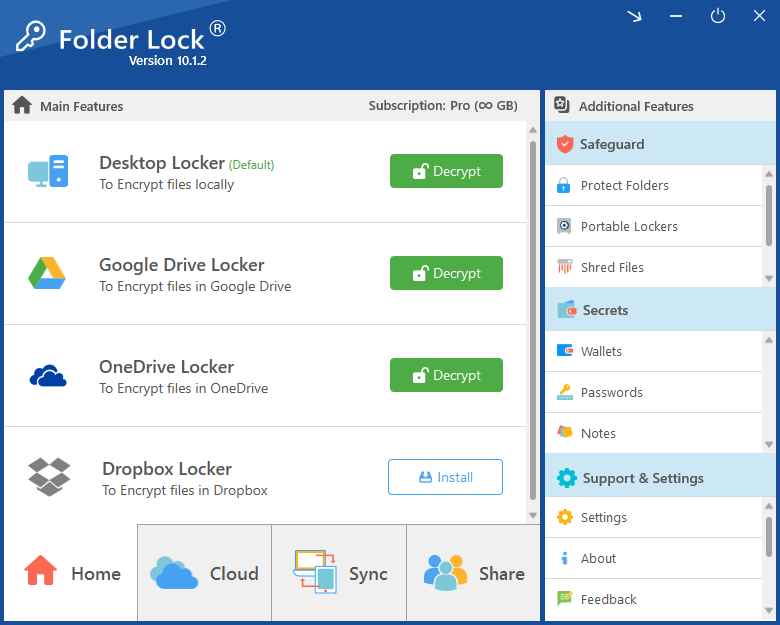
Start with a Desktop Locker for local protection or connect a supported cloud service to build a locker that syncs securely across devices.
The product emphasizes usability. In practice, your locker behaves like a familiar destination, helping users work with secure storage without needing complex manual steps each time.
Folder Lock’s core value is client-side protection. Files are encrypted on your device, helping keep cloud providers or compromised remote systems from seeing plain-text content.
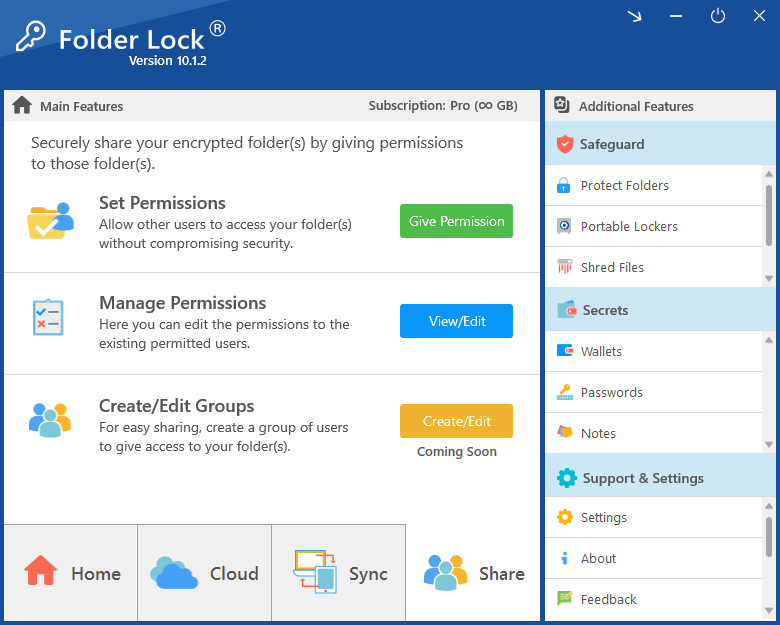
Once content is encrypted, users can sync it to supported services or share encrypted files with approved recipients through the product’s controlled access workflow.
Technical details
Security pages often lose conversions because they either oversimplify everything or overload visitors with raw specs. This section balances both.
Folder Lock highlights AES 256-bit encryption for data lockers and secrets. For users, that means private files are transformed into unreadable ciphertext before they are exposed to cloud infrastructure or shared storage.
The lock-and-hide feature is aimed at people who do not always want full encryption overhead. Folder Lock references a kernel-level driver for hiding and protecting files, folders, and drives, including in Safe Mode.
Client-side encryption is the key privacy message. Files are encrypted before they reach Dropbox, Google Drive, or OneDrive, helping limit exposure even if remote systems are compromised.
The key idea for visitors: cloud convenience does not have to mean handing over plain-text files.
Folder Lock also includes privacy cleanup tools, not just storage protection. That matters because deleted files and user history can still leak sensitive information when left behind.
Available locker types
Folder Lock 10 is not limited to a single encrypted container style. It offers multiple locker types for different privacy habits.
For users who want a local encrypted vault on their Windows PC with no dependency on cloud storage.
Designed for Dropbox users who want encrypted files synced without giving up their familiar storage ecosystem.
Protect content before it enters Google Drive so synced data stays encrypted from the source.
Keep Microsoft-centric workflows but add an extra client-side privacy layer to synced files.
Use mobile synchronization to keep protected content reachable across supported devices.
Carry encrypted containers on removable media for flexible transport and secure handoff.
Beyond file lockers
Instead of leaving sensitive information inside browser notes, text files, or random screenshots, Folder Lock adds a dedicated “Secrets” area for organized privacy.
Keep credit card details, banking information, and important private records inside an encrypted structure.
Save passwords inside a protected vault for backup and privacy-focused personal storage.
Write private notes, business details, or personal records in an encrypted note system rather than plain files.
Free vs Pro
Use the toggles below to compare what casual users get for free and what power users unlock with the Pro version.
Folder Lock Free
Entry-level privacy with 1 GB locker capacity and limited sync.
Folder Lock Pro
Full feature access for users who want deeper protection, sharing, and portability.
| Feature | Free | Pro |
|---|---|---|
| Locker Size | 1 GB | Unlimited |
| Sync Devices | 2 Devices | 5 Devices |
| Share Users | Not included | Unlimited |
| Mobile Apps | Included | Included |
| Secrets | Included | Included |
| Portable Lockers | Not included | Included |
| Protect Folders | Not included | Included |
| Shred Files | Included | Included |
| Clean History | Included | Included |
| Price | $0 | $39.95 |
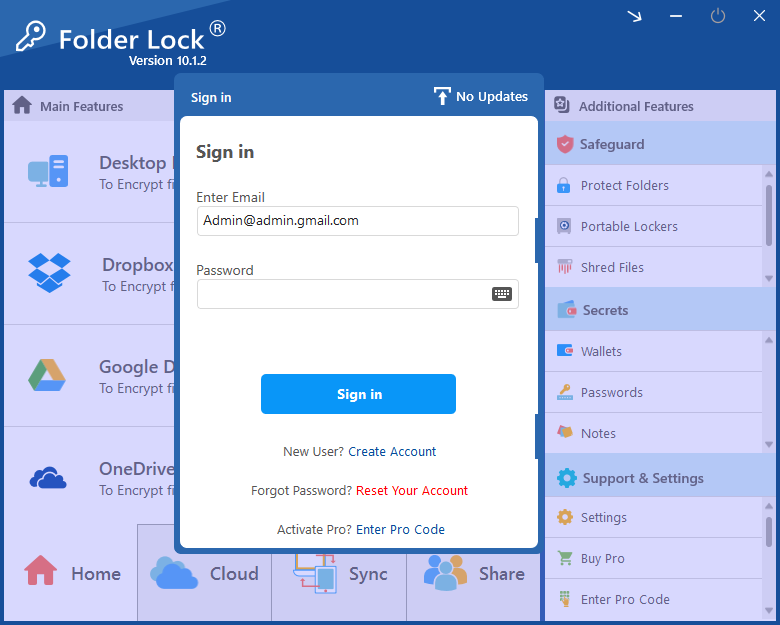
Product screenshots
These screenshots help visitors quickly understand the desktop dashboard, locker setup flow, and sharing controls before downloading.
Frequently asked questions
Each answer is written in plain language while preserving the technical intent behind the product’s privacy features.
Folder Lock focuses on client-side protection. Files placed inside supported lockers are encrypted with AES 256-bit encryption before they are synced or stored elsewhere. The product also offers a lock-and-hide option for users who want restricted visibility and access controls.
Yes. The product materials describe locker support for Dropbox, Google Drive, and OneDrive, allowing users to keep their encrypted files synced while maintaining privacy at the device level.
Portable lockers let users carry encrypted data on external media. This is helpful when you want to transport private content or share a protected container with someone you trust to use the correct password.
No. It also includes secure notes, wallets, password storage, file shredding, empty-space wiping, and Windows history cleanup. That makes it closer to a privacy toolkit than a single-purpose encryption utility.
It is useful for anyone who wants stronger personal privacy for work files, home documents, synced cloud folders, portable media, and sensitive notes without relying only on a cloud provider’s built-in security model.
Ready to secure your data?
This landing page is structured to convert by answering visitor objections early: what it does, how it works, what makes it technical, and why it matters in cloud-connected life.